Zero-trust access for real-world operations — Partner with VPNIUM
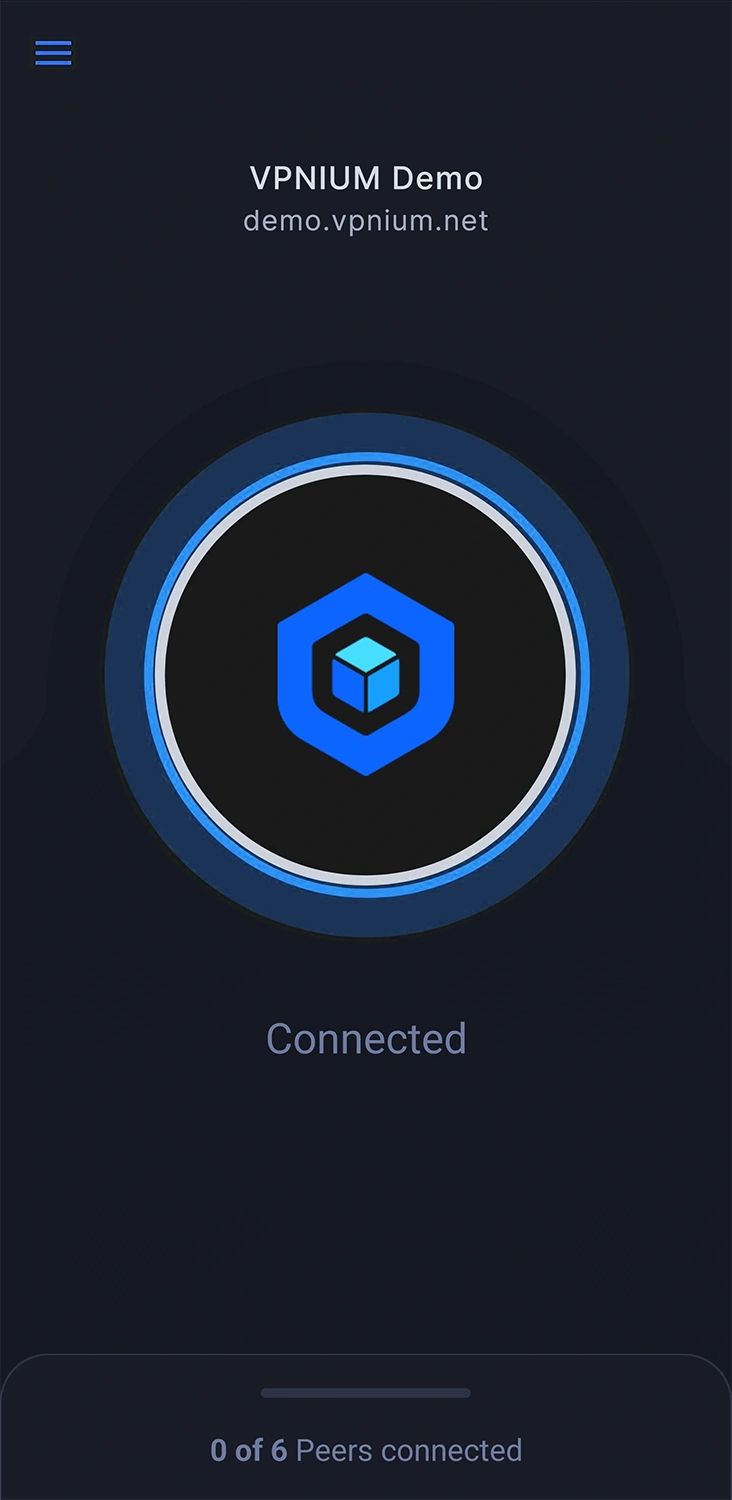
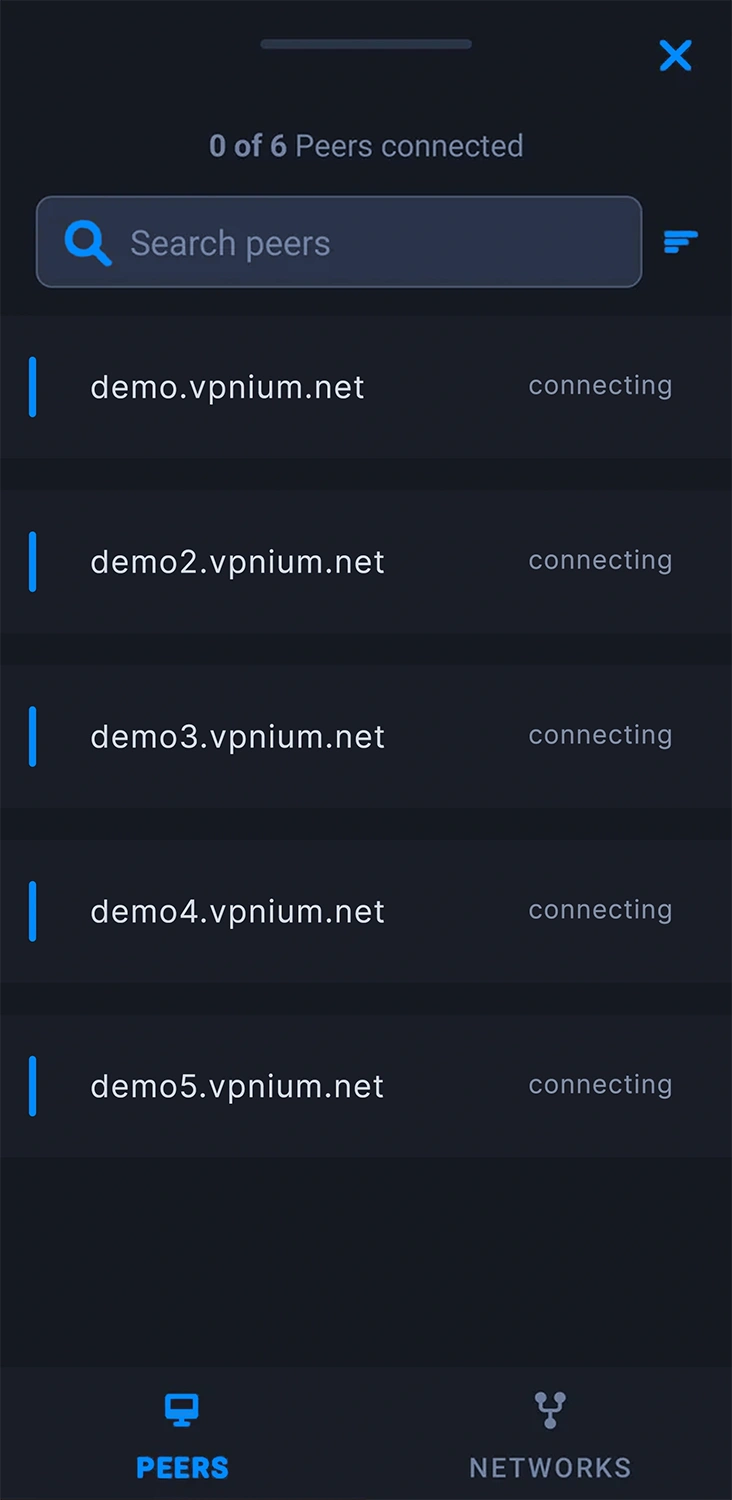
Connect people to apps and data—not to your whole network. VPNIUM applies continuous verification and fine-grained policies so remote work and multi-cloud stay fast to deploy and simple to govern.
Stand up gateways where you already operate—public cloud, hybrid, or your own footprint. Pick regions and providers that match latency, residency, and compliance without re-architecting the way you work.
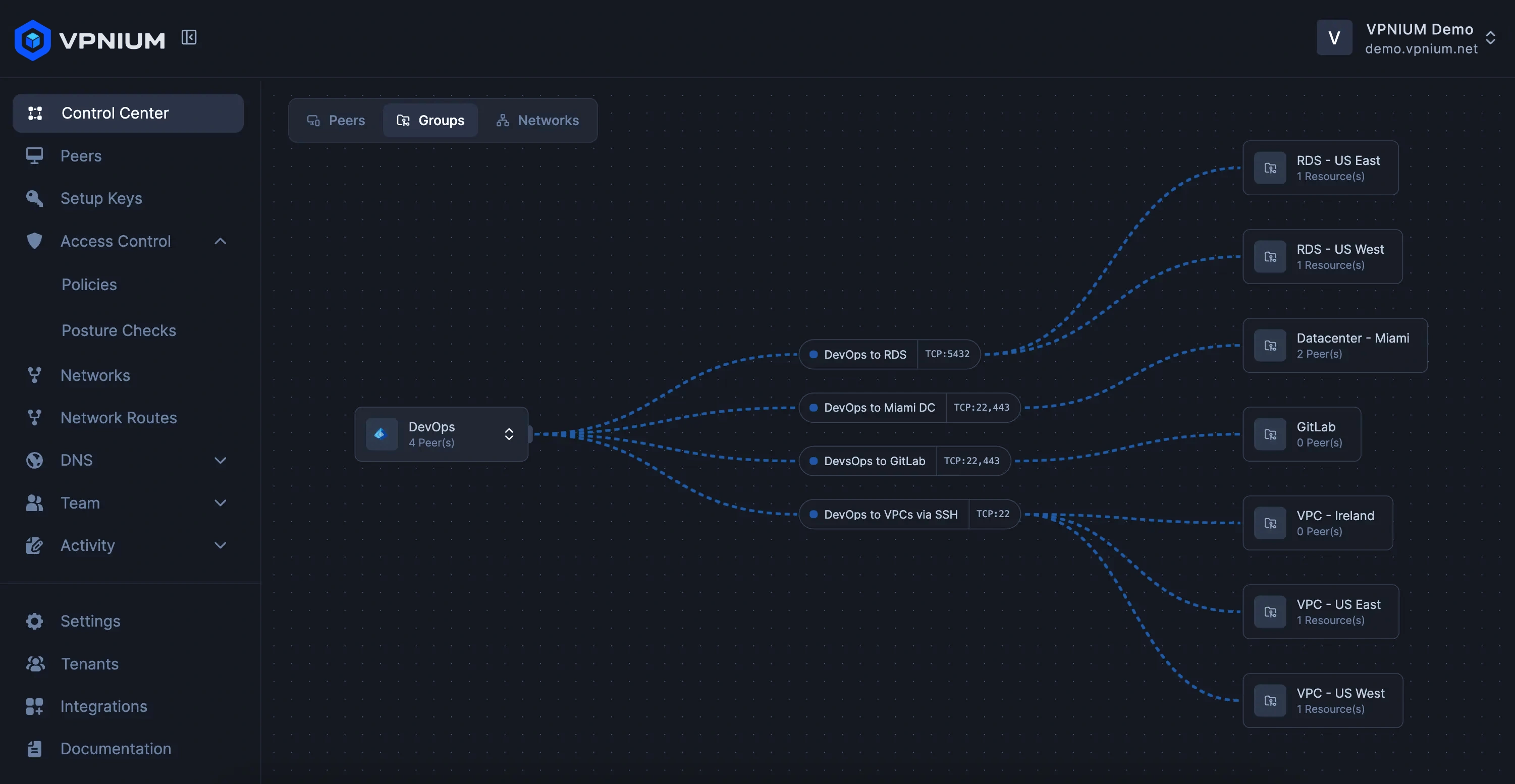
Map who may reach which applications, segments, and APIs—not entire subnets. Policies follow identities, groups, and context so every session starts from “no” and earns a precise “yes.”
Keep sessions encrypted end-to-end and workloads logically separated. When something looks off, containment is automatic—shrinking blast radius without slowing legitimate traffic.
Employees, contractors, and partners reach approved applications through encrypted tunnels that never dump them onto a flat corporate LAN—so coffee-shop Wi‑Fi stops being a board-level worry.
One console covers onboarding, policy changes, and visibility. Fewer bespoke scripts and firewall tickets mean your team ships access faster and audits it without archaeology.
Anchor enforcement close to users and workloads across AWS, Azure, Google Cloud, Hetzner, and more. Mix providers per region while keeping policy and telemetry consistent everywhere.
Pair identities, device posture, and business roles with application-level rules. Least privilege becomes the default posture—not a quarterly review slide.
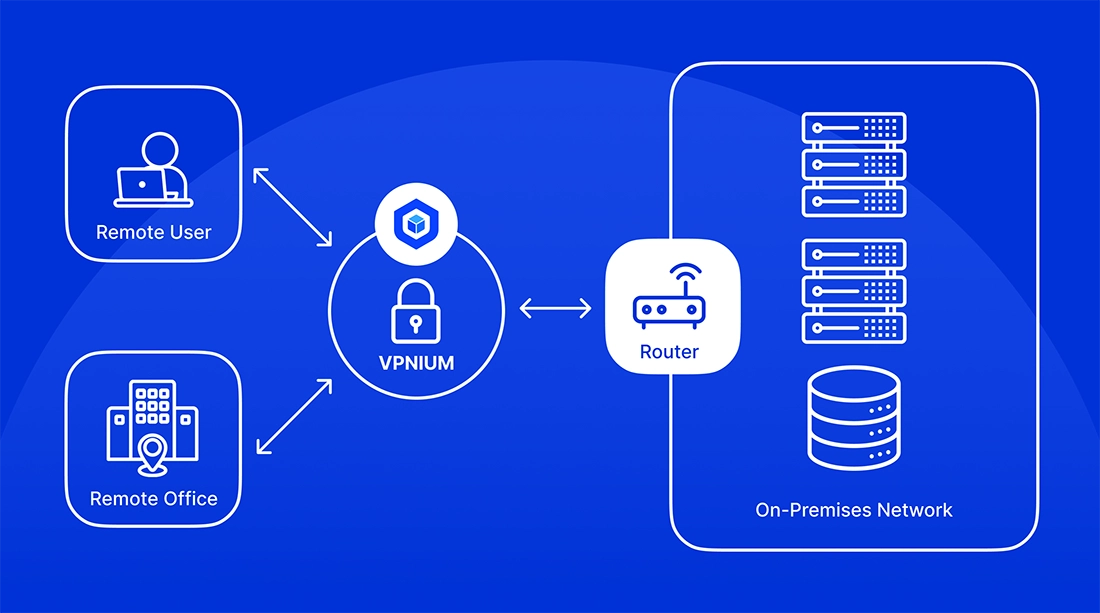
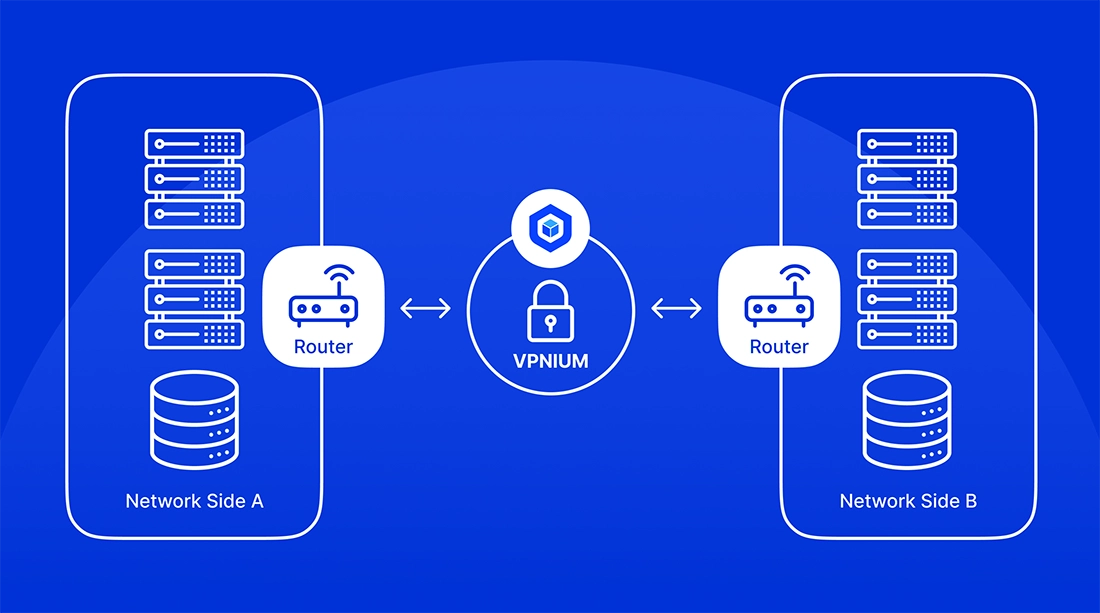
Link offices, factories, and partner networks with modern tunnels that inherit the same policy engine as your users—no parallel VPN stack to babysit.
Ring-fence sensitive traffic on isolated infrastructure when regulations or SLAs demand it—without giving up the unified policy model the rest of the org relies on.
Drop lightweight connectors onto hardware you already trust—data centers, telco POPs, or regulated enclaves—so sensitive flows never leave the footprint you certify.
Scale consumption with real adoption instead of shelf-ware licenses. Forecast spend from live telemetry and right-size capacity as teams grow or projects wind down.
Every request is evaluated on identity, device health, and policy before packets flow. Implicit trust disappears, replaced by continuous evidence—not quarterly firewall audits.
Express intent once—who can reach what—and let enforcement follow users and apps as they move. Policy travels with the session instead of living in a static VLAN map.
Layer strong authentication on top of contextual checks so stolen passwords alone cannot pivot your network. Integrate with the IdPs you already standardized on.

When something breaks at 2 a.m., you need responders who already know your topology. Our in-house team spans multiple continents, pairs directly with builders, and stays accountable until the incident is closed—not until a ticket ages out.
What you can expect:
Still comparing architectures? Start here—then reach out if you want a deeper dive tailored to your stack.
ZTNA replaces “connect first, ask questions later” VPNs with per-application admission. Users and devices prove who they are, meet posture checks, and only then receive narrowly scoped connectivity—dramatically shrinking what an attacker can touch if credentials leak.
Default deny is real, not a marketing line. Verified identities unlock only the applications and segments policy allows, administrators manage everything from a single pane, and telemetry makes drift obvious before it becomes an incident.
Hardware VPNs tax budgets and talent: bespoke tunnels, brittle HA pairs, and consultants on speed-dial. VPNIUM is delivered as a managed service with predictable scaling, centralized policy, and fewer moving parts—so your team ships access instead of babysitting boxes.
No. The same controls that satisfy regulated enterprises help lean IT teams punch above their weight. Start with the workloads that hurt most—remote engineering, partner extranets, or cloud admin access—and expand as your comfort grows.
You work with specialists who know the product roadmap—not scripted call centers. Coverage spans English, Spanish, and Italian time zones, and responses stay human: clear owners, transparent timelines, and follow-through until you are unblocked.
Yes. MSPs, integrators, and VARs can deliver VPNIUM as part of managed security offerings with co-selling support, onboarding assets, and a path to recurring revenue. Tell us about your practice—we will match you with the right enablement track.